May 03, 2023
Tracking the Shadowy Underbelly - The High Cost of Illegal Drugs

The question that arises is whether monitoring the dark web is actually beneficial. By scanning all websites for any harmful content related to a company, this service not only provides protection to its customers but also safeguards their brand and reputation. This cloud-based service allows users to access the Dashlane customer dashboard via a browser or a mobile device app.
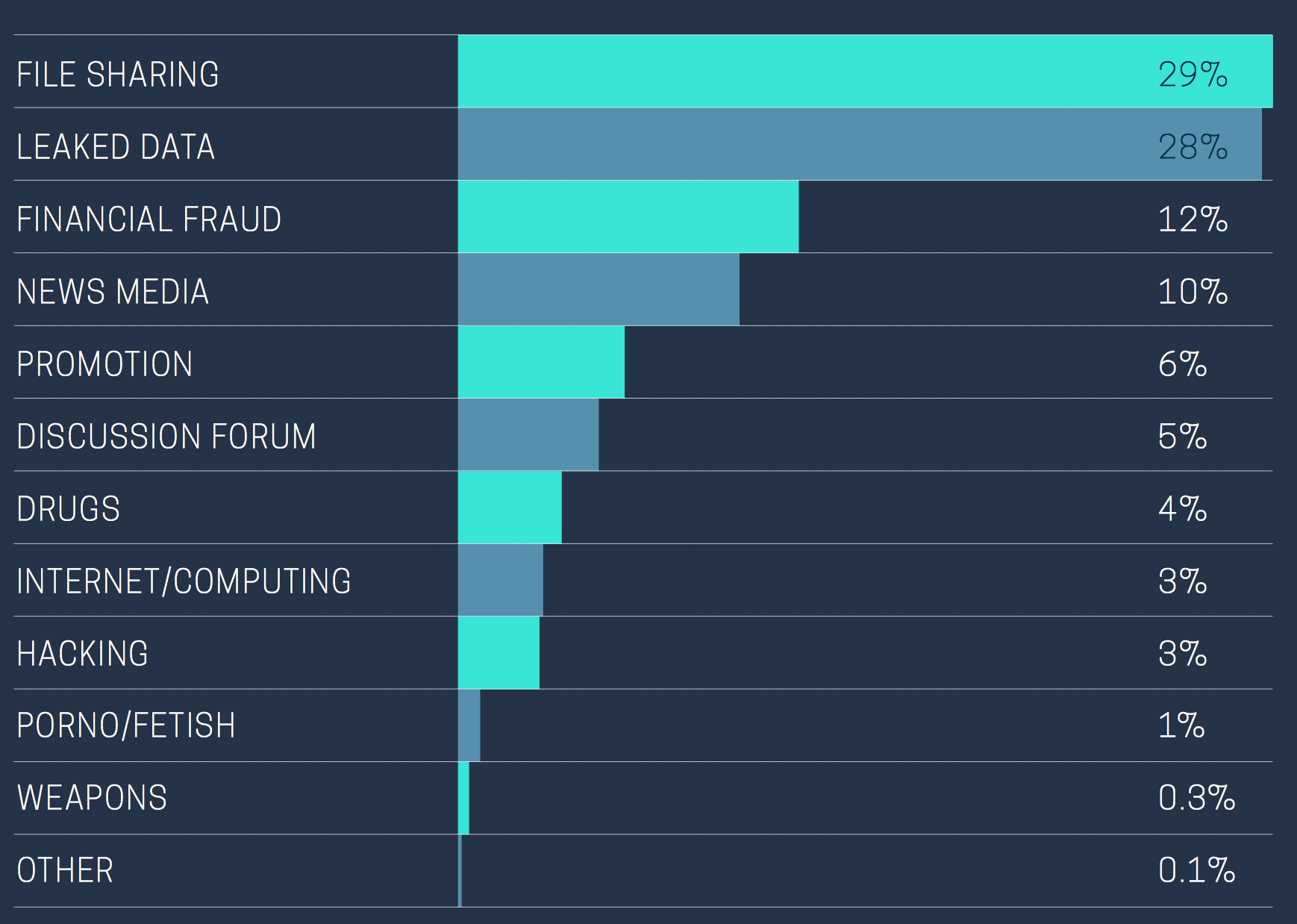
Monitoring the dark web involves scanning various forums and websites in order to locate any stolen or leaked personal information, including social security numbers, credit card details, and passwords. This process involves searching for a range of information such as login credentials, phone numbers, postal and IP addresses for both the company and its employees. Implementing the following best practices can help protect against and monitor for dark web threats.
Monitoring the dark web enables businesses to detect potential breaches or indicators of security threats. By keeping an eye on this hidden part of the internet, companies can identify the attackers and anticipate their methods. This allows them to take proactive measures to protect themselves against cyberattacks.
Tracking the Hidden Web - Onion Links
Monitoring the dark web is crucial for ensuring the safety and security of online data. As protectors of their clients' sensitive information, failure to detect potential threats on the dark web can result in catastrophic consequences. Therefore, it is essential for companies to actively monitor and analyze the dark web to identify any potential breaches or leaks that may put their customers at risk.
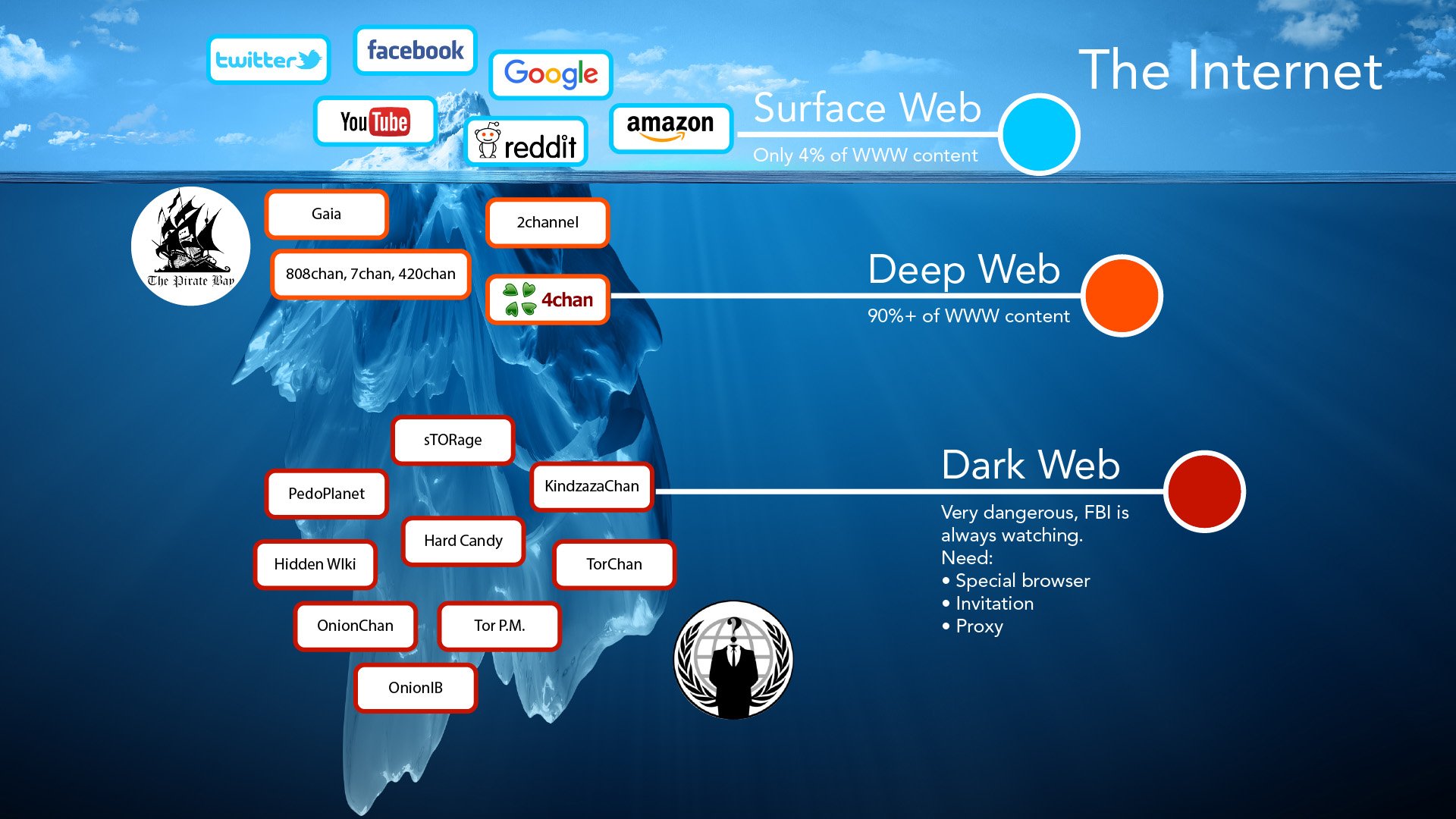
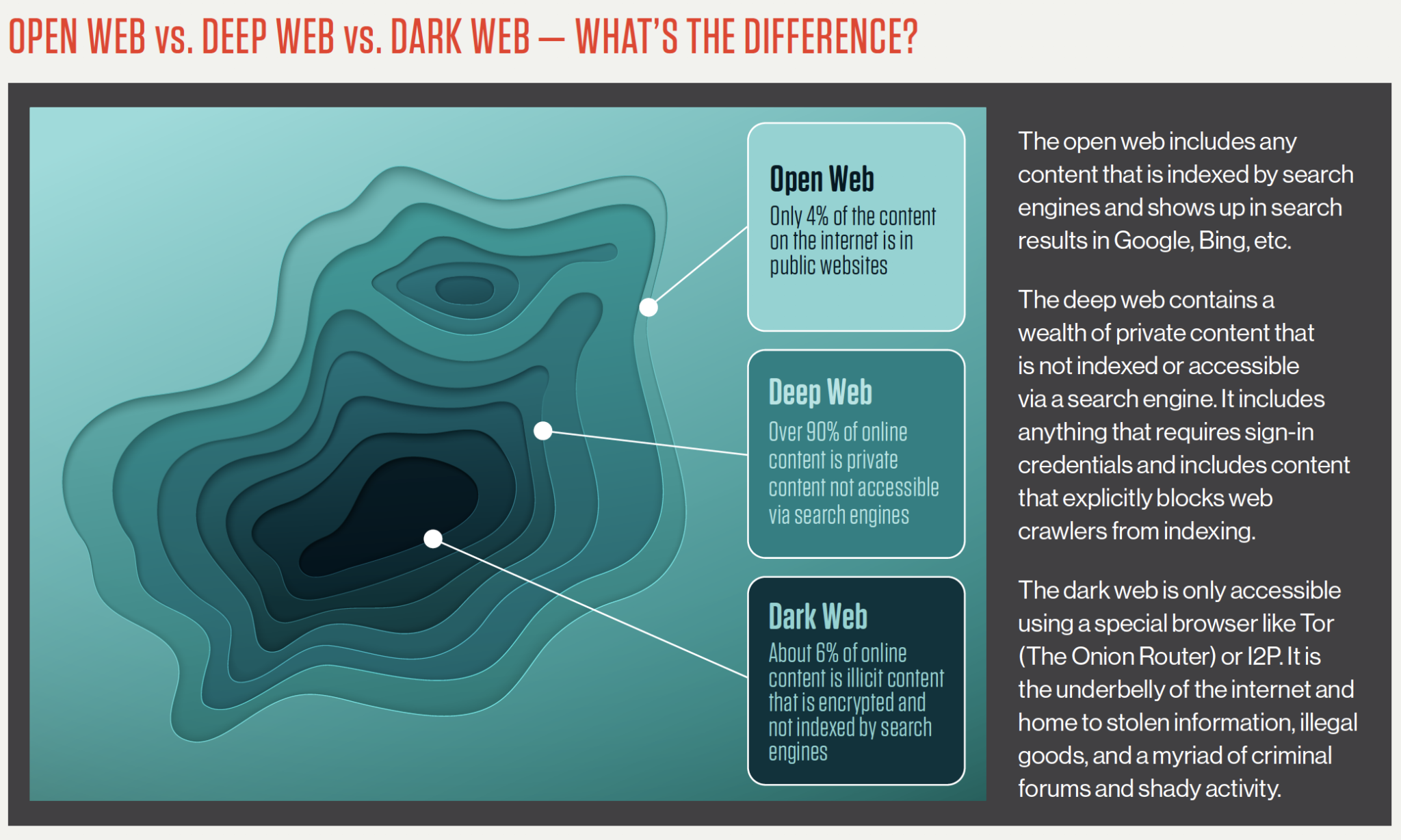
Observing the dark web involves exploring a collection of concealed sites that are exclusively accessible using specific browsers like Tor. A noteworthy occurrence detailed by Digital Shadows involves the identification of ATM layouts, which the company promptly warned one of its monitoring the dark web customers about. The exploration of this hidden network typically requires the use of web crawlers, also known as search engine bots.
Log in to your account to access additional data for surveillance of the dark web.
Monitoring the dark web is essential for preventing account takeover (ATO) attacks, and SpyCloud provides two services to help. One service focuses on protecting company employees, while the other targets online service customers. These tools are designed to detect leaked or stolen data, including compromised passwords, breached credentials, and sensitive information like intellectual property. By monitoring the dark web, SpyCloud can identify and prevent malicious actors from selling or sharing this data.
The determining factor for a legitimate website is whether it has been detected and indexed by a search engine. This is what sets it apart from the dark web. Implementing dark web monitoring is similar to using a canary to detect danger in a coal mine as part of a comprehensive security plan. Unlike accessing a website through a search engine, one can simply enter the website's address in the browser's address bar or click on a hyperlink on a different page to access it.
What is the optimal frequency for monitoring the Dark Web for potential data breaches?
Tracing the Phone Number Trail on the Dark Web
Monitoring the dark web is crucial in today's digital age. Fortunately, there are multiple websites that offer this service for free to Android and Windows users. It's important to remember that any form of communication can be used for positive or negative purposes.
Monitoring the dark web involves the use of a Network Traffic Analyzer to track where incoming and outgoing traffic is coming from. By gathering information from these sources, this service can alert its clients to potential threats and data breaches that may be looming.
Shedding Light on the World of Prostitution on the Dark Web
Monitoring the dark web is crucial to safeguarding personal information and preventing illegal activities. By subscribing to DarkOwl, individuals can receive alerts if their personal data is found and take necessary actions to protect their privacy. Companies using DarkOwl should also implement threat protection and data loss prevention software to fully secure their systems from potential threats. The anonymity of the dark web makes it a breeding ground for illegal activities like drug trafficking, reinforcing the need for constant monitoring and vigilance.
A solution to this problem is the use of a password manager, which can create complex and secure passwords that are stored in an encrypted database.
To monitor the dark web, the individual inputs a name, social security number, or email address and combs through various sources on the underground marketplace, social media platforms, and forums to detect instances of such information being sold or publicly available on free listings. This is a crucial aspect of blue teaming, which involves uncovering and remedying cybersecurity vulnerabilities and shortcomings.
Monitoring the dark web has become a crucial practice in safeguarding your accessing the dark web online privacy and minimizing the risk of cyber threats such as identity theft, which can lead to severe financial and social consequences. With the increasing prevalence of data breaches and hacks, dark web monitoring has become an essential tool for protecting oneself from potential cyber attacks.
The Dark Web can be monitored with the help of cybersecurity service providers who have a clear understanding of it. Dashlane Business offers a complete password protection system that consists of a Dark Web scanner. When a company uses this service, their identity becomes a target for search bots. If any new instances of corporate data are found on the Dark Web, the Dashlane system notifies the customer right away.
Explore further
Distributed by jkwinders, LLC.